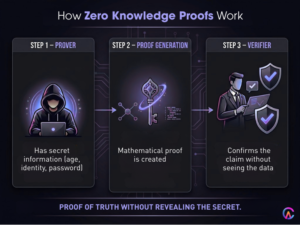
Zero knowledge proofs (ZKPs) allow one party to prove the truth of a statement to another without disclosing any underlying data, which helps maintain privacy and confidentiality. This is crucial for maintaining a competitive edge and ensuring regulatory compliance while achieving mathematical certainty and verifiable computation. ZKPs are scalable and have significant applications in Web3 and enterprise settings. Technologies like zk SNARKs, zk STARKs, PLONK, recursive proofs, and bulletproofs are the backbone of platforms like Zcash, Tornado Cash, and Ethereum layer 2 rollups, including zk Rollups, Polygon, Hermez, and Scroll. They enable confidential smart contracts, private DeFi, voting systems, and identity solutions, allowing for age verification and credit score eligibility without exposing any personal data.
Semantic clustering and topical authority around zero knowledge proofs help clarify search intent, comparing zk SNARKs and zk STARKs, and discussing ZKP blockchain privacy as we look ahead to 2026. The scalability of zk rollups is driving featured snippets in SERPs, while AI generated answers are optimizing answer engines with signals of Experience, Expertise, Authoritativeness, and Trustworthiness (EEAT). This clarity is essential for privacy preserving computation and confidential smart contracts.
In contrast, traditional authentication methods like passwords, social security numbers, and credit card details often expose sensitive information, increasing the risks of identity theft and fraud. ZKPs, on the other hand, allow for the proof of knowledge possession, such as a private key or age verification, and creditworthiness without revealing any data. This approach not only preserves user sovereignty and supports data minimization but also aligns with GDPR compliance and offers quantum resistance.
Zero Knowledge Proof Fundamentals Mathematical Cryptography Privacy
Zero knowledge proofs cryptographic protocols enable verifier statement truth without conveying additional information beyond statement validity three core properties completeness soundness zero knowledge. Completeness honest prover convinces honest verifier valid statement soundness dishonest prover convinces honest verifier invalid statement probability negligible zero knowledge verifier learns nothing beyond statement validity preserving information theoretic security computational assumptions.
Interactive proofs require communication rounds verifier challenges to prove non interactive proofs NIZK single proof verifiable independently preserving scalability blockchain applications public verification gas optimization. Succinct non interactive arguments knowledge SNARKs short proofs fast verification constant size independent witness complexity preserving layer 2 rollup scalability Ethereum mainnet settlement.
ZKP core properties mathematical guarantees privacy
- Completeness: An honest prover can convince an honest verifier of valid statements.
- Soundness: A dishonest prover can only convince the verifier of invalid statements with negligible probability.
- Zero knowledge: The verifier learns nothing beyond the validity of the statement.
- Non interactive proofs: A single proof allows for public verification, enhancing blockchain scalability.
- Succinctness: Constant size proofs enable fast verification and improve layer 2 efficiency.
Ultimately, ZKPs strike a balance between information theoretic privacy and computational efficiency, making them vital for trillion dollar applications like confidential transactions and private voting systems..
zk SNARKs Zero Knowledge Succinct Non Interactive Arguments Knowledge
zk SNARKs elliptic curve pairings quadratic arithmetic programs QAP trusted setups powers Zcash shielded transactions Tornado Cash private Ethereum transfers confidential DeFi protocols achieving sub millisecond proof generation verification 1-2 kilobyte proof sizes. Pinocchio libsnark Groth16 most deployed SNARK constructions trusted setup ceremonies multi party computation MPC secure randomness preserving toxic waste parameter generation collusion resistance.
Trusted setup compromise reveals proving verification keys enabling fake proofs mitigated MPC ceremonies hundreds participants burning toxic waste preserving cryptographic security confidence. Proof aggregation recursive SNARKs verify multiple proofs single proof preserving verification aggregation layer 2 rollup scalability Ethereum settlement efficiency.
zk SNARK advantages deployment maturity limitations
- Sub millisecond proof generation and verification with 1 to 2 KB proof sizes
- Efficient elliptic curve pairings and QAP trusted setups
- Battle tested maturity with Zcash and Tornado Cash for confidential DeFi
- Recursive aggregation for verifying multiple proofs with a single verification, boosting scalability
- Trusted setup MPC ceremonies that ensure collusion resistance while managing toxic waste
The power of zk SNARKs fuels the production of ZK rollups and supports confidential applications, all while maintaining a mature ecosystem and seamless tooling for Solidity integration.
zk STARKs Scalable Transparent Arguments Knowledge Quantum Resistance
zk STARKs utilize hash based FRI for fast Reed Solomon interactive oracle proofs, eliminating the need for a trusted setup while ensuring quantum resistance and post quantum security. These proofs can range from 10 to 50 KB in size, which may lead to longer verification times of 1 to 10 milliseconds, all while maintaining transparency and allowing for permissionless deployment. StarkWare’s Cairo, STARKDEX, and StarkNet are all part of the Ethereum layer 2 scaling solutions, along with Circle’s STARK identity solutions and StarkWare’s validity rollups, which uphold scalability, transparency, and quantum security.
Collision resistant hash functions and FRI polynomial commitment schemes facilitate a permissionless setup, enabling anyone to generate verification keys while preserving decentralization and eliminating the need for trusted third parties. The Algebraic Intermediate Representation (AIR) supports general purpose computation with RISC V VMs, ensuring compatibility with smart contracts and EVM equivalence.
zk STARK advantages quantum resistance transparency
- Hash based FRI allows for no trusted setup and supports permissionless deployment.
- Post quantum security is achieved through lattice based hash function resistance.
- Larger proofs, ranging from 10 to 50 KB, come with longer verification times, presenting scalability trade offs.
- AIR and RISC V enable general purpose computation while maintaining EVM compatibility.
- Transparency and decentralization are upheld through permissionless proving and verification keys.
In summary, zk STARKs not only ensure quantum resistance and transparency but also support general purpose computation, paving the way for a future proof ZK infrastructure.
PLONK Permutations over Lagrange bases for Scalable Verification
PLONK offers a universal trusted setup through a single ceremony that accommodates multiple circuits, allowing for custom preprocessing while maintaining flexibility in proving key generation for various applications, all under one trusted setup. With KZG polynomial commitments, we achieve efficient recursion and aggregation, enhancing the settlement efficiency of layer 2 rollups on the Ethereum mainnet.
Universal setup MPC ceremonies facilitate the creation of circuit specific proving keys, which not only preserve the reusability of the proving system but also boost developer productivity across multiple ZK applications, all while requiring just a single infrastructure investment.
PLONK advantages universal setup flexibility
- A single ceremony for a universal trusted setup that supports multiple circuits
- Custom preprocessing for circuit specific proving keys, enhancing flexibility
- Efficient recursion and aggregation through KZG polynomial commitments
- Reusability of the proving system, improving developer productivity and infrastructure efficiency
- Optimization of settlement through Ethereum layer 2 rollup batching
PLONK strikes a balance between the efficiency of SNARKs and the transparency of STARKs, creating a production ready universal proving system.
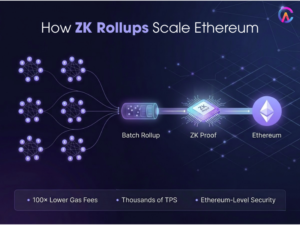
ZK Rollups Scalability Privacy Ethereum Layer 2 Solutions
ZK rollups are a game changer for Ethereum, allowing thousands of transactions to be bundled into a single ZK proof. This not only compresses the state on Ethereum’s Layer 1 but also ensures data availability and execution privacy, all while being compatible with the EVM. With these rollups, users can enjoy a staggering 100x savings on gas fees and achieve throughput of up to 1000 transactions per second. Projects like Polygon, Hermez, Scroll, and zkSync Era are leading the charge by batching transactions and generating SNARK and STARK proofs that verify on Ethereum, maintaining finality, security, and economic guarantees while promoting decentralization.
Validity proofs ensure that the state transition functions are executed correctly, providing a cheat proof settlement and maintaining the security guarantees of Layer 1. This means that Ethereum can scale effectively while preserving its integrity. Recursive proofs take it a step further by aggregating multiple rollup proofs into a single Ethereum proof, optimizing verification and enhancing interoperability across multiple rollups.
ZK rollup advantages Ethereum scaling privacy
- Enjoy 100x gas savings and 1000 TPS with EVM compatibility and execution privacy.
- Validity proofs ensure cheat proof settlements while upholding Layer 1 security guarantees.
- Data availability is enhanced through compression and batching efficiency on Ethereum’s Layer 1.
- Recursive aggregation boosts multi rollup interoperability and verification gas efficiency.
- Projects like Polygon, Hermez, Scroll, and zkSync Era are already making strides in production deployments.
ZK rollups are paving the way for Ethereum’s scalability and privacy, supporting a billion dollar total value locked in Layer 2 infrastructure.
Privacy Preserving Applications Confidential Smart Contracts DeFi
Confidential smart contracts are designed to execute private states with private inputs while allowing for public verification. This approach helps maintain the confidentiality of business logic, giving companies a competitive edge in areas like supply chain finance, private auctions, and sealed bid voting systems. In the realm of Private DeFi, protocols focus on confidential lending, borrowing, and margin trading options, all while ensuring privacy and adhering to regulatory compliance, including KYC and AML requirements, which is crucial for institutional adoption.
When it comes to identity solutions, we’re talking about age verification and credit score eligibility that prove authenticity without exposing sensitive data. This aligns with data minimization principles and GDPR compliance, promoting self sovereign identity (SSI) through decentralized identifiers (DIDs) and verifiable credentials (VCs).
Privacy applications enterprise Web3 use cases
- Confidential smart contracts that maintain private state and business logic confidentiality
- Private DeFi options for lending, margin trading, and ensuring regulatory compliance
- Identity solutions focusing on age verification and credit score data minimization through SSI
- Private voting mechanisms, sealed bid auctions, and supply chain finance
- Confidential stablecoins for enterprise treasury management and compliance
Zero Knowledge Proofs (ZKPs) are paving the way for enterprise Web3 adoption by preserving privacy, ensuring compliance, and enhancing scalability for trillion dollar applications
ZK Machine Learning Privacy Preserving Inference Training
ZK machine learning is proving to be a game changer for model inference, especially when it comes to handling private inputs and model weights. This technology is making strides in healthcare diagnostics, financial scoring, and fraud detection while ensuring confidential computation. With zk ML frameworks like ezkl and DeepGem, we can leverage TensorFlow and PyTorch models alongside ZK proofs to maintain verifiable AI in healthcare and financial credit scoring.
Fully homomorphic encryption (FHE) combined with zk ML hybrid approaches is key to preserving input privacy and model confidentiality, especially for inference verification in regulated industries like healthcare and finance.
ZK ML applications verifiable confidential computation
- Healthcare diagnosis, financial scoring, and fraud detection with private inference
- Utilizing ezkl, DeepGem, and zkML with TensorFlow and PyTorch for on chain AI
- FHE and zk ML hybrid methods ensure input and model confidentiality while meeting compliance
- Verifiable AI model governance guarantees tamper-proof predictions
- Adhering to compliance requirements in regulated industries like HIPAA, GDPR, and SOC2
ZK ML is all about fostering trustworthy AI in regulated sectors, ensuring model governance, compliance, and scalability.
Performance Optimization Proving Verification Gas Costs
The optimization cycle for proof systems involves folding lookup arguments, working with multilinear polynomials, and using custom gates to ensure sub millisecond performance, all while achieving 100x gas savings through verification aggregation and batching. We leverage hardware acceleration with GPUs, FPGAs, and ASICs to create specialized ZK proving circuits that maintain hyperscale throughput, reaching millions of transactions per second in cloud proving services.
When it comes to selecting proof systems, we consider circuit size, proving time, and verification gas tradeoffs to ensure application specific optimizations, including rollups, SNARKs, identity STARKs, and machine learning with PLONK, all while balancing efficiency and maturity.
Performance optimization production deployment
- Cycle folding lookup arguments and the efficiency of multilinear polynomials
- Hardware acceleration through GPUs, FPGAs, and ASICs for hyperscale throughput
- Verification aggregation and batching that achieves 100x gas savings for Ethereum settlements
- Circuit specific optimizations for rollups and identity in machine learning applications
- Cloud proving services that ensure enterprise scalability and robust infrastructure
Our optimization efforts are designed to maintain a production ready ZK infrastructure for hyperscale applications, instilling confidence in billion dollar total value locked (TVL) projects.
Quantum Resistance Post Quantum Cryptography Migration
Quantum computers pose a challenge to elliptic curve cryptography, including ECDSA, ed25519, and SNARK pairings, all of which are vulnerable to Shor’s algorithm. On the other hand, lattice based and hash based STARKs offer some quantum resistance. The NIST post quantum cryptography standards, like lattice based CRYSTALS, Kyber, and Dilithium, along with hash based SPHINCS, are paving the way for secure systems that can withstand quantum threats.
We’re seeing a gradual shift towards hybrid EC lattice signatures that maintain quantum resistance while ensuring backward compatibility and long term security for applications worth trillions, especially in DeFi and identity infrastructure.
Quantum resistance post quantum migration
- Lattice based standards like CRYSTALS, Kyber, Dilithium, and hash based SPHINCS
- STARKs as quantum resistant proof systems
- Hybrid EC lattice signatures that support backward compatibility
- NIST PQC standards for enterprise compliance and long term security
- Protecting trillion dollar applications in DeFi and identity infrastructure
Ultimately, quantum resistance is crucial for preserving the long term viability of zero knowledge proofs (ZKPs) and ensuring a secure post quantum Web3 infrastructure.
How Codearies Helps Customers Implement Zero Knowledge Proof Systems
Codearies is all about delivering top notch enterprise grade ZK proof platforms, including zk SNARKs, STARKs, PLONK, ZK rollups, and confidential smart contracts. We’re talking about zk ML privacy preserving applications that can achieve millions of transactions per second with sub millisecond proving for billion dollar total value locked in production deployments.
zk SNARK STARK PLONK proving infrastructure
Our trusted setup involves MPC ceremonies, universal PLONK, recursive aggregation, and GPU acceleration, all while ensuring sub millisecond proving and verification. This means we can handle hyperscale throughput and enterprise level scalability.
ZK rollups Ethereum layer 2 privacy scalability
With Polygon, Hermez, Scroll, and zkSync, we offer validity proofs, data availability, EVM compatibility, and impressive gas savings, 100 times less. Plus, we can manage 1000 TPS for confidential execution while maintaining Ethereum’s settlement security.
Confidential smart contracts private DeFi identity
We also focus on private state execution for confidential lending and borrowing, SSI age verification, credit scoring, and zk ML applications in healthcare and finance, all while ensuring compliance and fostering enterprise Web3 adoption.
ZK machine learning verifiable confidential inference
Our ezkl DeepGem zkML integrates seamlessly with TensorFlow and PyTorch, ensuring HIPAA, GDPR, and SOC2 compliance for verifiable AI model governance and tamper proof predictions in regulated industries.
Quantum resistant post quantum ZK infrastructure
We utilize lattice based STARKs that meet NIST PQC standards for hybrid migration, ensuring the long term security of trillion dollar applications and the viability of post quantum Web3.
Frequently Asked Questions
Q1: What are the fundamental differences between zk SNARKs and zk STARKs?
SNARKs rely on elliptic curve pairings and require a trusted setup, allowing for quick verification. On the other hand, STARKs are based on hashes, are transparent, quantum resistant, and can handle larger proofs. Codearies is implementing SNARKs, STARKs, and PLONK for optimized, application specific production deployments.
Q2: What are the advantages of ZK rollups in terms of scalability and privacy for Ethereum?
ZK rollups can achieve 100 times the gas efficiency and 1000 transactions per second, thanks to validity proofs and data availability. They also ensure EVM compatibility and enable confidential execution while maintaining security through L1 settlement. Codearies is actively building ZK rollups for Polygon, Hermez, and Scroll as part of their layer 2 infrastructure.
Q3: How do confidential smart contracts enhance private DeFi applications?
These contracts allow for private state execution, enabling confidential lending and borrowing while ensuring business logic adheres to privacy and regulatory compliance, which is crucial for enterprise adoption. Codearies is delivering confidential smart contracts tailored for private DeFi and SSI compliance platforms.
Q4: How is ZK machine learning being applied in verifiable AI for healthcare and finance?
With private inference and model weights, these solutions comply with HIPAA and GDPR, providing tamper proof predictions for regulated industries. Codearies is implementing zkML and ezkl with DeepGem to create a verifiable AI compliance infrastructure.
Q5: What does quantum resistance mean for post quantum ZK migration?
It involves using lattice based STARKs and NIST PQC, along with hybrid elliptic curve lattice signatures, to ensure long term security worth trillions. Codearies is focused on building quantum resistant ZK infrastructure to ensure the viability of Web3 in a post quantum world.
For business inquiries or further information, please contact us at